Merged
Conversation
- [x] elasticsearch - [x] lambda-layer-node-proxy-agent - [x] ecr-assets - [x] opensearchservice - [x] chatbot - [x] lambda-layer-kubectl - [x] appmesh - [x] lambda - [x] lambda-destinations ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
instead of assuming `aws` partition, use the stack to determine partition (which will result in a reference to `AWS::Partition`) fixes #18429 ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
CDK Pipelines generates a number of CodeBuild projects, and they are hard to tell apart some times. Add `Description` fields to each of them. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
prev: hashicorp/terraform-provider-aws#22453, #18110 ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
…Patterns (#18157) This PR introduces changeable ports as a regression fix for the hardcoded port 80 in both NLB constructs bases. Closes #18073 Additionally it seems like the regression reported in the linked issue was not spotted in the integration tests either. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
Add conditions matcher to assertion package. Required by #18560. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
Co-authored-by: AWS CDK Team <aws-cdk@amazon.com> Co-authored-by: mergify[bot] <37929162+mergify[bot]@users.noreply.github.com>
I’m trying to use the new format=esm bundling with NodejsFunction I noticed that it bundles the “CJS” version of dependencies not the ESM version (if available). esbuild has some wack defaults - https://esbuild.github.io/api/#main-fields This causes problems because the CJS versions usually have stuff like require() and they don’t work for tree-shaking. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
Fixes: #18443 *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
Depends on #18577 ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
…mplete (#18536) There are [upcoming changes](https://aws.amazon.com/blogs/compute/coming-soon-expansion-of-aws-lambda-states-to-all-functions/) that will rollout Lambda states to all Lambda Functions. Prior to this update (current functionality) when you made an `updateFunctionCode` request the function was immediately available for both invocation and future updates. Once this change is rolled out this will no longer be the case. With Lambda states, when you make an update to a Lambda Function, it will not be available for future updates until the `LastUpdateStatus` returns `Successful`. This PR introduces a custom waiter that will wait for the update to complete before proceeding. The waiter will wait until the `State=Active` and the `LastUpdateStatus=Successful`. The `State` controls whether or not the function can be invoked, and the `LastUpdateStatus` controls whether the function can be updated. Based on this, I am not considering a deployment complete until both are successful. To see a more in depth analysis of the different values see #18386. In my testing I found that the time it took for a function to go from `LastUpdateStatus=InProgress` to `LastUpdateStatus=Successful` was: - ~1 second for a zip Function not in a VPC - ~25 seconds for a container Function or a Function in a VPC - ~2 minutes to deploy a VPC function (best proxy for StateReasonCode=Restoring) There are a couple of built in waiters that could have been used for this, namely [functionUpdated](https://docs.aws.amazon.com/AWSJavaScriptSDK/latest/AWS/Lambda.html#functionUpdated-waiter). This waiter uses `getFunctionConfiguration` which has a quota of 15 requests/second. In addition the waiter polls every 5 seconds and this cannot be configured. Because hotswapping is sensitive to any latency that is introduced, I created a custom waiter that uses `getFunction`. `getFunction` has a quota of 100 requests/second and the custom waiter can be configured to poll every 1 second or every 5 seconds depending on what type of function is being updated. fixes #18386 ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
Closes #18508. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
The logs monitor test was using `Date.now()` which sometimes caused the actual result to differ from the expected result. Turns out the reason I needed the dynamic date is because I was generating the timestamp incorrectly. Fixed that which allowed me to use a hardcoded timestamp. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
fixes #18575 Models documentation for [similar](https://docs.aws.amazon.com/cdk/api/v1/docs/@aws-cdk_aws-ec2.VpcAttributes.html) [structs](https://docs.aws.amazon.com/cdk/api/v1/docs/@aws-cdk_aws-lambda.FunctionAttributes.html) ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
…odePipeline (#18530) This adds support for importing a ECS Cluster via the Arn, and not requiring the VPC or Security Groups. This will generate an ICluster which can be used in `Ec2Service.fromEc2ServiceAttributes()` and `FargateService.fromFargateServiceAttributes()` to get an `IBaseService` which can be used in the `EcsDeployAction` to allow for cross account/region deployments in CodePipelines. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
This PR is proposed by #17711. The first step of the roadmap in #17711 is implemented in this PR. > 1. implement DetectorModel and State with only required properties > - It will not be able to have multiple states yet. If this PR is merged, the simplest detector model can be created as following: 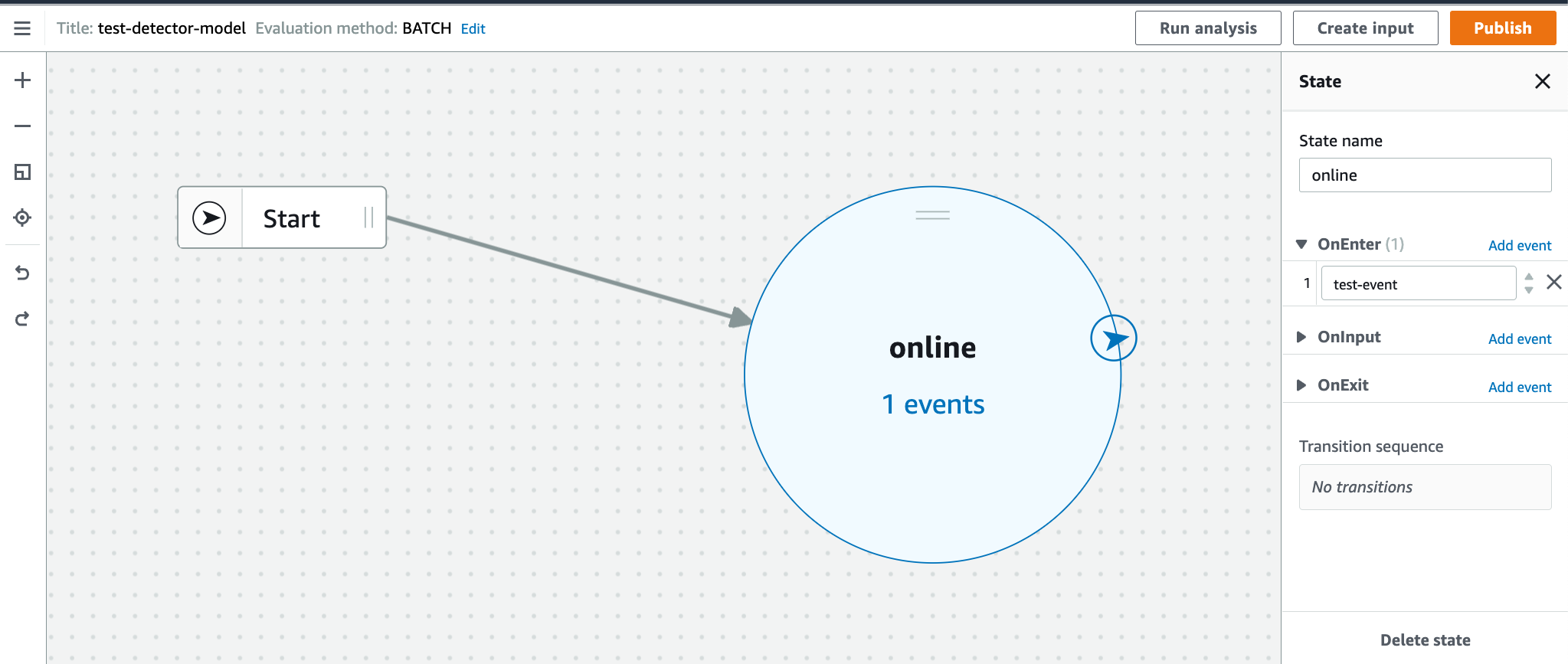 ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
Co-authored-by: AWS CDK Team <aws-cdk@amazon.com>
---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
- cognito - acmpca - codeguruprofiler - cloud9 - signer ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
…ore customization (#18561) ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
When using synthetics runtime "syn-nodejs-puppeteer-3.1" the default role tries to call s3:getBucketLocation on the artifacts bucket, but the policy is incorrect to allow that action. The policy should allow for that call directly on the bucket arn. fixes #13572 ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
Looking to unblock users who want to use assertions with annotations added on a stack. Fixes #18347 Example: ```ts class MyAspect implements IAspect { public visit(node: IConstruct): void { if (node instanceof CfnResource) { this.warn(node, 'insert message here', } } protected warn(node: IConstruct, message: string): void { Annotations.of(node).addWarning(message); } } const app = new App(); const stack = new Stack(app); new CfnResource(stack, 'Foo', { type: 'Foo::Bar', properties: { Baz: 'Qux', }, }); Aspects.of(stack).add(new MyAspect()); AssertAnnotations.fromStack(stack).hasMessage({ level: 'warning', entry: { data: 'insert message here', }, }); ``` ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
…18311) Adds an option to DnsValidatedCertificate to automatically cleanup the related DNS validation records when the Certificate is deleted. This is an opt-in property and discouraged for production use, as there are edge cases that can cause unintended side effects. The most obvious is that if two or more certificates exist with the same domain, the same validation record is used for both. If one certificate is deleted (and deletes the validation record), the second certificate (with the same domain name) will be unable to automatically renew. closes #3333 closes #7063 ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
In "special" regions (GovCloud, US-ISO), the CodeDeploy service principal uses the `amazonaws.com` DNS suffix. In fact, that is true of all regions, in all partitions, with the notable exception of `aws-cn` which uses the `amazonaws.com.cn` suffix instead. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
* feat: cloudformation spec v53.1.0 * chore(servicediscovery): adding awslint exception Co-authored-by: AWS CDK Team <aws-cdk@amazon.com> Co-authored-by: Nick Lynch <nlynch@amazon.com> Co-authored-by: mergify[bot] <37929162+mergify[bot]@users.noreply.github.com>
Closes #18175 - see #18175 (comment) for details. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
Amazon RDS for PostgreSQL supports new minor versions 13.5, 12.9, 11.14, 10.19, and 9.6.24. https://aws.amazon.com/about-aws/whats-new/2022/01/amazon-rds-postgresql-amazon-rds-outposts-postgresql-minor-versions/ ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
…/assert (#18634) ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
We're about to deprecate `assert-internal` and `cdk-integ-tools` only uses `canonicalizeTemplates`. There is an argument for canonicalizing assets by default in `assertions` as well, but I am putting that on the backlog for now. For now, just copying over the relevant function which will remove the dependency to `assert-internal`. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
…teway (#18595) To pass the Task Token in headers to an API Gateway, the token must be wrapped in an array (because that's the value type of headers). Because JSONPath evaluation needs to happen to resolve the token, we need to use the `States.Array()` function in a `JsonPathToken` to properly resolve this. However, doing that makes the existing validation code fail the validation checking that you are passing the task token somewhere. Add convenience methods for the intrinsics, and update the checker to also find paths referenced inside intrinsic functions. Fixes #14184, fixes #14181. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
…nd `grantPut` methods (#18494) In this pull request I try to fix a big behavioral change in the bucket grant methods for write actions. This change was introduced due to security issues as stated in [this pull request](#12391) and substituted the `s3:PutObject*` action glob pattern with the simple `s3:PutObject` to exclude the dangerous `s3:PutObjectAcl` and `s3:PutObjectVersionAcl` from the equation. While I agree about the security issues, I think that other useful actions - if safe, obviously - should be added when calling the `grantWrite`, `grantReadWrite` and `grantPut` methods. This pull request adds the following actions: * s3:PutObjectLegalHold * s3:PutObjectRetention * s3:PutObjectTagging * s3:PutObjectVersionTagging I also added the `s3:PutObjectVersionAcl` action to the `grantPutAcl` method, along with the existing `s3:PutObjectAcl`. I adapted existing unit and integ tests to accept these new actions. Fixes #13616 ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
* Assign `aws-ecr-assets` to `madeline-k` to align with her ownership of `aws-ecr`. * Assign `assets` to `otaviomacedo` to align with his ownership of `aws-s3` * Assign `aws-lambda-layer-kubectl` to `otaviomacedo` to align with his ownership of `aws-eks`. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
# Overview Replace usage of `-p` with `--project` for `dotnet run` to resolve deprecation warning (`NETSDK1174`). This appears during AWS CDK usage under .NET (C#, F#). The full error message is similar to the following example: > The abbreviation of -p for --project is deprecated. Please use --project. > The use of -p in dotnet run is deprecated because of the close relationship dotnet run has with dotnet build and dotnet publish. In dotnet build and dotnet publish, p is used to set MSBuild properties. This deprecation is the first step in aligning abbreviations for these three commands. Resolves #18092 # References See https://docs.microsoft.com/en-us/dotnet/core/tools/sdk-errors/netsdk1174 ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
The autolabeler will not perform on issues with priority labels anymore Additionally, any issues which don't fall into a specific area will be automatically assigned to the DSEs ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
Co-authored-by: AWS CDK Team <aws-cdk@amazon.com>
The Route53 HealthCheckConfig structure is modeled in the CloudFormation spec as a JSON blob, but it was previously modeled as an explicit structure (see structure, as it's not updated with the Route53 spec. This adds the missing RoutingControlArn to the structure. fixes #18570 ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
In #18150, a change was merged that blew up the size of the inline Lambda beyond its limit of 4096 characters. This change was not detected because the Lambda constructs being used there didn't use the regular `aws-lambda` module, but escape hatches that bypass the regular validation (released in 1.139.0, 2.8.0). Because this effectively broke S3 notifications, it was rolled back in #18507 (released in 1.140.0, not yet released in 2.x line). In this PR, add validation to make sure an event like this doesn't happen again. This will be relevant for #18614. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
Ran npm-check-updates and yarn upgrade to keep the `yarn.lock` file up-to-date.
…ase labels (#18288) Skipping validation in case the `props.releaseLabel` is unresolved. ---- *By submitting this pull request, I confirm that my contribution is made under the terms of the Apache-2.0 license*
Co-authored-by: AWS CDK Team <aws-cdk@amazon.com>
rix0rrr
approved these changes
Jan 27, 2022
Contributor
|
🙏 |
Contributor
|
Thank you for contributing! Your pull request will be automatically updated and merged without squashing (do not update manually, and be sure to allow changes to be pushed to your fork). |
Collaborator
Author
AWS CodeBuild CI Report
Powered by github-codebuild-logs, available on the AWS Serverless Application Repository |
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
See CHANGELOG