APPLICATIONS
HOT NEWS
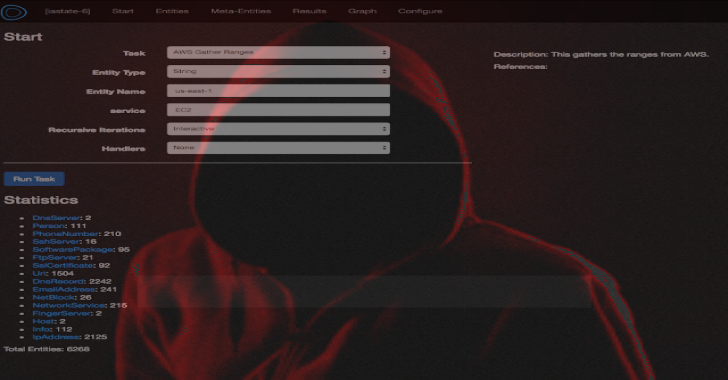
Intrigue Core : Discover Your Attack Surface
Intrigue Core is a framework for external attack surface discovery and automated OSINT. There are a number of use cases:
Application and Infrastructure (Asset) DiscoverySecurity...
© kalilinuxtutorials.com 2025