cli: support SQL disk spilling in tenants#71040
cli: support SQL disk spilling in tenants#71040craig[bot] merged 1 commit intocockroachdb:masterfrom
Conversation
 jaylim-crl
left a comment
jaylim-crl
left a comment
There was a problem hiding this comment.
Reviewable status:
complete! 0 of 0 LGTMs obtained (waiting on @andy-kimball and @darinpp)
pkg/cli/mt_start_sql.go, line 71 at r1 (raw file):
// at the time of writing stateless and may not be provisioned with // suitable storage. serverCfg.Stores.Specs = nil
We can remove this safely now since we already default to logging to stderr:
cockroach/pkg/cli/log_flags.go
Lines 78 to 82 in bc42b66
pkg/cli/mt_start_sql.go, line 91 at r1 (raw file):
} // Initialize the target directory for temporary storage. If encryption at
Taken from
Lines 442 to 472 in bc42b66
 jaylim-crl
left a comment
jaylim-crl
left a comment
There was a problem hiding this comment.
Also tested this on CC with --max-disk-temp-storage=50MiB, and it seems to work as intended:
$ cockroach sql --url '...' -e 'select trunc(random()*1000000000)::int as name from generate_series(1, 100000000) order by name;'
ERROR: temp disk storage: disk budget exceeded: 1048576 bytes requested, 52428800 currently allocated, 52428800 bytes in budget
SQLSTATE: 53100
Failed running "sql"
Reviewable status:
complete! 0 of 0 LGTMs obtained (waiting on @andy-kimball and @darinpp)
 knz
left a comment
knz
left a comment
There was a problem hiding this comment.
Reviewed 2 of 2 files at r1, all commit messages.
Reviewable status:complete! 0 of 0 LGTMs obtained (waiting on @andy-kimball and @darinpp)
pkg/cli/mt_start_sql.go, line 91 at r1 (raw file):
Previously, jaylim-crl (Jay Lim) wrote…
Taken from
Lines 442 to 472 in bc42b66
Could you extract this code into a common function and call it from both places.
3858392 to
aaf5203
Compare
 jaylim-crl
left a comment
jaylim-crl
left a comment
There was a problem hiding this comment.
TFTR!
Reviewable status:
complete! 0 of 0 LGTMs obtained (waiting on @andy-kimball, @darinpp, and @knz)
pkg/cli/mt_start_sql.go, line 91 at r1 (raw file):
Previously, knz (kena) wrote…
Could you extract this code into a common function and call it from both places.
Done.
 knz
left a comment
knz
left a comment
There was a problem hiding this comment.
Reviewed 2 of 2 files at r2, all commit messages.
Reviewable status:complete! 0 of 0 LGTMs obtained (waiting on @andy-kimball and @darinpp)
|
TFTR! bors r=knz |
|
Build failed: |
|
bors r+ |
|
Build failed: |
Previously, temp storage for SQL tenants was configured to point to memory with a limit of 100MB. As a result, all ephemeral data when processing large queries end up going to memory, and there was no way to configure this to point to disk. This commit changes that behavior, and the default temp storage for SQL tenants is now the same as SQL for dedicated, i.e. disk, with a limit of 32GB. The operator can configure this through the `--max-disk-temp-storage` flag. Release note (cli change): `cockroach mt start-sql` will now support the following flags to configure ephemeral storage for SQL when processing large queries: `--store`, `--temp-dir`, and `--max-disk-temp-storage`. Release note (sql change): SQL tenants will now spill to disk by default when processing large queries, instead of memory.
aaf5203 to
af5a5a5
Compare
|
bors r+ |
|
Build succeeded: |
In cockroachdb#71040 we added disk spilling which in particular added the following call to the `mt start-sql` code path: https://github.com/cockroachdb/cockroach/blob/af5a5a5065ce80c5e6568b4b422bf5c3a179e173/pkg/cli/mt_start_sql.go#L90-L89 The tenant doesn't support the `--store` flag, and so this will always be the default of `cockroach-data`. This has the unfortunate effect of trying to clean up the temp dirs for that directory, even if `--temp-dir` is supplied: https://github.com/cockroachdb/cockroach/blob/6999e5fded43f59eb5839dc8b943fd1e2a33a3fd/pkg/cli/start.go#L223-L227 In the `multitenant-upgrade` roachtest, as it happens there was actually a cockroach host instance running under `cockroach-data`, and so the tenant would fail to try to remove its (locked) temp dirs. This commit fixes that issue by making start-sql use an in-memory store spec. This fixes the test flake, but I wonder if the temp storage feature for tenants is working properly. I worry about this because the concept of a "temp engine" always seems to require a store: https://github.com/cockroachdb/cockroach/blob/6999e5fded43f59eb5839dc8b943fd1e2a33a3fd/pkg/cli/start.go#L274-L280 and I am not sure how deep this goes. Frankly I don't understand why if you are providing a Path you also need to provide a StoreSpec. I will leave untangling this to @knz and @jaylim-crl, who know this code better than I do. Fixes cockroachdb#69920. Release note: None
In cockroachdb#71040 we added disk spilling for tenants which added the following call to the `mt start-sql` code path: https://github.com/cockroachdb/cockroach/blob/af5a5a5065ce80c5e6568b4b422bf5c3a179e173/pkg/cli/mt_start_sql.go#L90-L89 The defaults for the store match that of a regular CockroachDB node, and the tenant will thus attempt to clean up temp dirs for `cockroach-data` if no store is specified: https://github.com/cockroachdb/cockroach/blob/6999e5fded43f59eb5839dc8b943fd1e2a33a3fd/pkg/cli/start.go#L223-L227 In the `multitenant-upgrade` roachtest, as it happens there was actually a cockroach host instance running under `cockroach-data`, and so the tenant would fail to try to remove its (locked) temp dirs. Fix that by passing the `--store` flag to the tenants in this test. This is mildly annoying since the predecessor version doesn't understand it and so the test has to figure out when it is legal to pass it. Anyway, it is done now. I will point out that it isn't the greatest choice to have tenants default to `cockroach-data` as the resulting interaction with a CRDB server results in an unfortunate UX. I filed cockroachdb#71603 to that effect. Release note: None
71604: roachtest: fix multitenant-upgrade r=jaylim-crl a=tbg In #71040 we added disk spilling for tenants which added the following call to the `mt start-sql` code path: https://github.com/cockroachdb/cockroach/blob/af5a5a5065ce80c5e6568b4b422bf5c3a179e173/pkg/cli/mt_start_sql.go#L90-L89 The defaults for the store match that of a regular CockroachDB node, and the tenant will thus attempt to clean up temp dirs for `cockroach-data` if no store is specified: https://github.com/cockroachdb/cockroach/blob/6999e5fded43f59eb5839dc8b943fd1e2a33a3fd/pkg/cli/start.go#L223-L227 In the `multitenant-upgrade` roachtest, as it happens there was actually a cockroach host instance running under `cockroach-data`, and so the tenant would fail to try to remove its (locked) temp dirs. Fix that by passing the `--store` flag to the tenants in this test. This is mildly annoying since the predecessor version doesn't understand it and so the test has to figure out when it is legal to pass it. Anyway, it is done now. I will point out that it isn't the greatest choice to have tenants default to `cockroach-data` as the resulting interaction with a CRDB server results in an unfortunate UX. I filed #71603 to that effect. Release note: None Co-authored-by: Tobias Grieger <tobias.schottdorf@gmail.com>
In #71040 we added disk spilling for tenants which added the following call to the `mt start-sql` code path: https://github.com/cockroachdb/cockroach/blob/af5a5a5065ce80c5e6568b4b422bf5c3a179e173/pkg/cli/mt_start_sql.go#L90-L89 The defaults for the store match that of a regular CockroachDB node, and the tenant will thus attempt to clean up temp dirs for `cockroach-data` if no store is specified: https://github.com/cockroachdb/cockroach/blob/6999e5fded43f59eb5839dc8b943fd1e2a33a3fd/pkg/cli/start.go#L223-L227 In the `multitenant-upgrade` roachtest, as it happens there was actually a cockroach host instance running under `cockroach-data`, and so the tenant would fail to try to remove its (locked) temp dirs. Fix that by passing the `--store` flag to the tenants in this test. This is mildly annoying since the predecessor version doesn't understand it and so the test has to figure out when it is legal to pass it. Anyway, it is done now. I will point out that it isn't the greatest choice to have tenants default to `cockroach-data` as the resulting interaction with a CRDB server results in an unfortunate UX. I filed #71603 to that effect. Release note: None
In #71040 we added disk spilling for tenants which added the following call to the `mt start-sql` code path: https://github.com/cockroachdb/cockroach/blob/af5a5a5065ce80c5e6568b4b422bf5c3a179e173/pkg/cli/mt_start_sql.go#L90-L89 The defaults for the store match that of a regular CockroachDB node, and the tenant will thus attempt to clean up temp dirs for `cockroach-data` if no store is specified: https://github.com/cockroachdb/cockroach/blob/6999e5fded43f59eb5839dc8b943fd1e2a33a3fd/pkg/cli/start.go#L223-L227 In the `multitenant-upgrade` roachtest, as it happens there was actually a cockroach host instance running under `cockroach-data`, and so the tenant would fail to try to remove its (locked) temp dirs. Fix that by passing the `--store` flag to the tenants in this test. This is mildly annoying since the predecessor version doesn't understand it and so the test has to figure out when it is legal to pass it. Anyway, it is done now. I will point out that it isn't the greatest choice to have tenants default to `cockroach-data` as the resulting interaction with a CRDB server results in an unfortunate UX. I filed #71603 to that effect. Release note: None
Previously, the `multitenant-upgrade` test had several workarounds and branches for dealing with predecessor versions less than v21.2, particularly the fact that these versions did not support the `--store` flag passed on the `mt start-sql` CLI command. This was introduced in cockroachdb#71040, and subsequently incorporated into the roachtest (including workarounds) in cockroachdb#71604. Now that the current version is v22.1, and thus the predecessor version supports the `--store` flag, it is necessary to remove the workaround in order to ensure proper functionality of the test. Additionally, this change cleans up an even earlier workaround for validating the cluster version for predecessor versions less than v21.1.2. Fixes cockroachdb#72971. Release note: None
72948: ui: add index stats to table details page r=lindseyjin a=lindseyjin Resolves #67647, #72842 Previously, there was no way to view and clear index usage stats from the frontend db console. This commit adds Index Stats tables for each table on the Table Detail pages, allowing users to view index names, total reads, and last used statistics. This commit also adds the functionality of clearing all index stats as a button on the Index Stats tables. 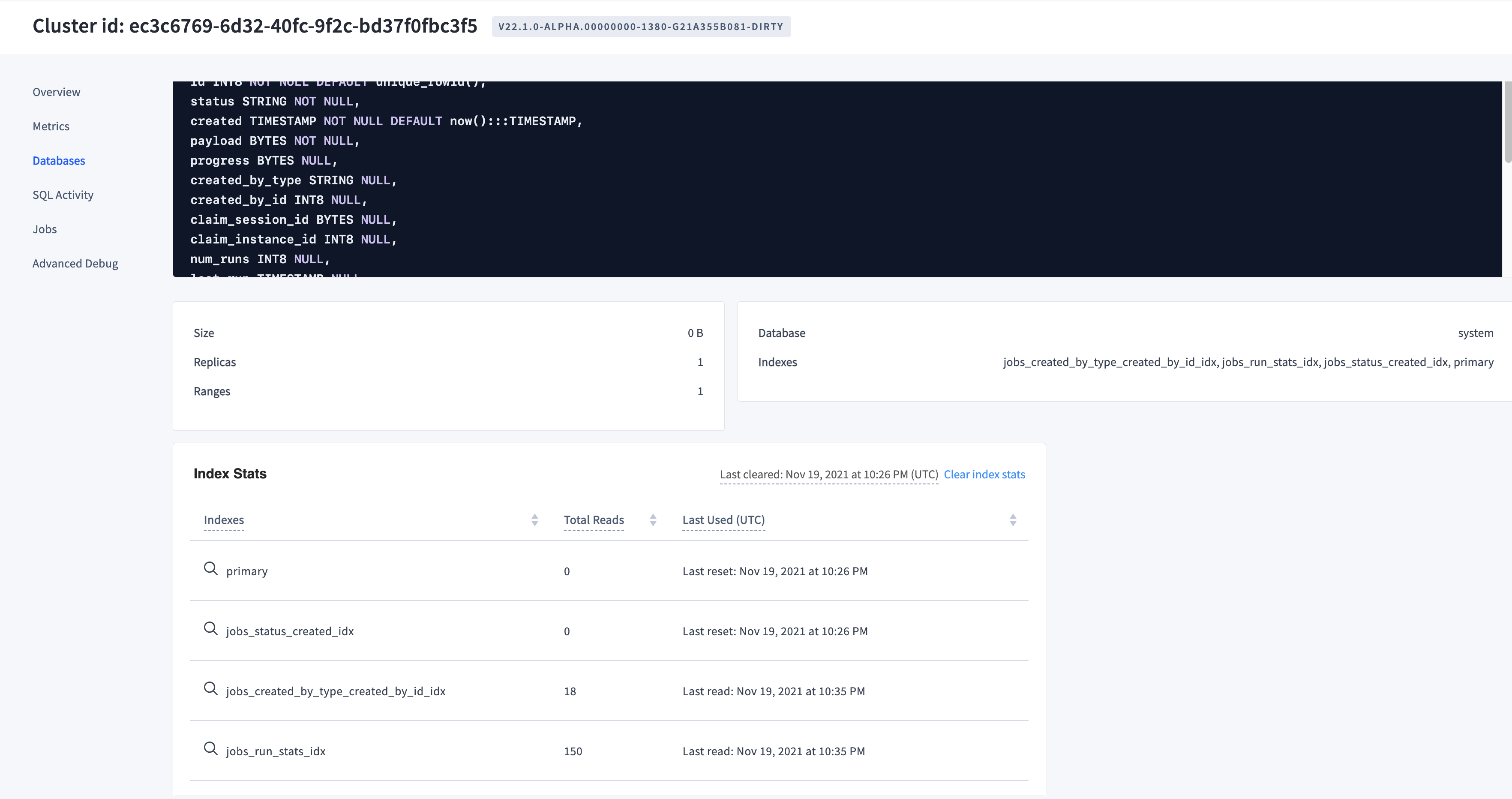 Release note (ui change): Add index stats table and button to clear index usage stats on the Table Details page for each table. 73145: roachtest: fix flags used in multitenant-upgrade for versions >= v21.2 r=AlexTalks a=AlexTalks Previously, the `multitenant-upgrade` test had several workarounds and branches for dealing with predecessor versions less than v21.2, particularly the fact that these versions did not support the `--store` flag passed on the `mt start-sql` CLI command. This was introduced in #71040, and subsequently incorporated into the roachtest (including workarounds) in #71604. Now that the current version is v22.1, and thus the predecessor version supports the `--store` flag, it is necessary to remove the workaround in order to ensure proper functionality of the test. Additionally, this change cleans up an even earlier workaround for validating the cluster version for predecessor versions less than v21.1.2. Fixes #72971. Release note: None Co-authored-by: Lindsey Jin <lindsey.jin@cockroachlabs.com> Co-authored-by: Alex Sarkesian <sarkesian@cockroachlabs.com>
Previously, temp storage for SQL tenants was configured to point to memory
with a limit of 100MB. As a result, all ephemeral data when processing large
queries end up going to memory, and there was no way to configure this to
point to disk. This commit changes that behavior, and the default temp storage
for SQL tenants is now the same as SQL for dedicated, i.e. disk, with a limit
of 32GB. The operator can configure this through the
--max-disk-temp-storageflag.
Release note (cli change):
cockroach mt start-sqlwill now support thefollowing flags to configure ephemeral storage for SQL when processing large
queries:
--store,--temp-dir, and--max-disk-temp-storage.Release note (sql change): SQL tenants will now spill to disk by default
when processing large queries, instead of memory.
Release justification: The upcoming Serverless MVP release plans to allow
spilling to ephemeral disk for SQL operations (See CC-4983), but the
existing
start-sqlfor tenants doesn't support that. This commit changesthe default spilling behavior in multi-tenant scenarios, and allows an operator
to configure ephemeral SQL storage through the CLI, and should have no
impact on dedicated customers.