I used git for the last few years in this context:
- Host = my laptop, windows.
- WSL enabled
- Repos live in the Linux side.
- I access them both from the Linux and the Windows side.
I can access the files in Linux either via git-bash like this (via the //wsl$/ share):
Or natively in the WSL bash terminal:
Those accesses go to the very same directory.
Error
Now it happens that if I do git status inside a repo from the windows side it gives the error fatal: detected dubious ownership in repository at:
While in the WSL-Linux it does not, for the same directory:
Since when?
It did not happen before. I've been using this setup for years. This started happening 2 days ago.
In fact, I installed a newer version of git-bash 2 days ago and I suspect the bash environment could condition this.
I work with about 100 repos, and I have found to fail in all of them which I've tried (about 10 repos). Expectedly it'll happen to those 100 repos.
None of those previously-working now-failing repos have been touched, so neither users, neither permissions have changed.
So mutating from "well" to "bad" is not in the filesystem side, must be in the git-bash side.
Problem
I don't want to just white-list it with safe.directory. I want to understand what's going on behind the scenes. Why it happens today and not 3 days ago. I want to know "what does git expect" and see how can I correct it.
Investigation so far
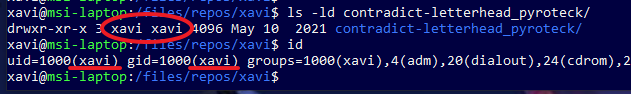
The users seem correct. From the linux side:
And from the windows side it also matches the hard disk and the id:
Question
How can I tell the ownership that is expected by git for it to do not complain?