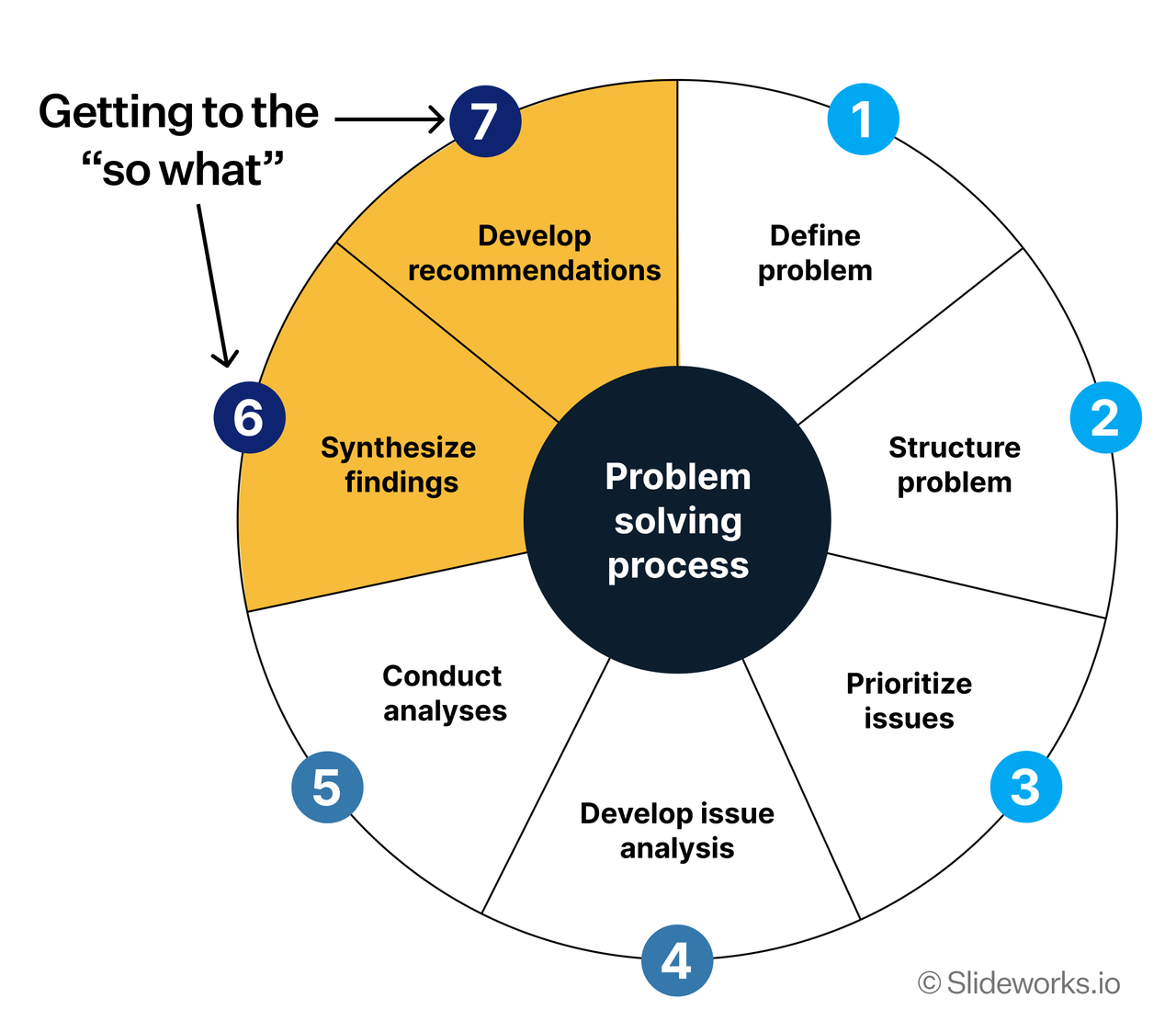
What is the problem?
Clearly define the problem you are trying to solve. Understand its scope, impact, and the desired outcome.
Break down the problem
Decompose the problem into smaller, manageable components. This helps in identifying the root causes and understanding the various aspects of the problem.
Prioritize issues
Identify the most critical issues that need to be addressed first. Focus on those that will have the most significant impact on solving the problem.
Develop hypotheses
Formulate potential solutions or hypotheses for each of the prioritized issues. These should be based on data, insights, and best practices.
Gather data
Collect relevant data to test your hypotheses. This may involve conducting research, analyzing existing data, or gathering new information.
Analyze data
Examine the data to validate or refute your hypotheses. Look for patterns, trends, and insights that can inform your decision-making.
Synthesize findings and recommend solutions
Summarize your findings and develop actionable recommendations based on your analysis. Present your solutions in a clear and concise manner, highlighting the benefits and potential risks.
Problem Statement Worksheet
To effectively define and understand the problem at hand, use the following Problem Statement Worksheet as your problem-solving framework. This tool helps in clarifying the key aspects of the problem before diving into the solution process.
- Basic Question to be Resolved: What is the core problem that needs to be
solved?
- Frame it as a clear and concise question.
- Context and Background: What is the situation that led to this problem?
- What happened previously that caused this issue to arise?
- Understanding the context helps in identifying relevant factors and scoping the answer appropriately.
- Decision Maker/Stakeholders: Who are the key individuals involved in
the decision-making process?
- No matter how good your strategy is, if no one buys in, it’s just talk on paper. For any action to be taken at the organizational level, it’s essential that all decision-makers and their stakeholders aren’t overlooked at least in the initial stages.
- Usually, the person raising the issue might not be the one making the final decision.
- You need to identify all relevant stakeholders to two groups:
- Decision Maker: The person who has the authority to make the final call.
- Decision Influencers: Individuals who can impact the decision-making process
through their opinions, expertise, or influence.
- Champions: People who actively support and promote the solution.
- Blockers: Individuals who may resist or oppose the solution.
- And then to make stakeholders analysis:
- Who must agree to the solution for it to be implemented successfully?
- Align with them ASAP, engage them and discuss with them early in the process.
- Study their preferences, concerns, and motivations, etc.
- What have they done in the past when faced with similar problems?
- What’s the relationship between them and other stakeholders?
- What’s their risk tolerance level?
- What’s their preferred communication style?
- What are their key performance indicators (KPIs) or success metrics?
- …
- Who shouldn’t disagree with the solution?
- Who aren’t important to the decision-making process?
- Who must agree to the solution for it to be implemented successfully?
- Criteria for Success: What are the key metrics or indicators (KPIs) that
will determine if the problem has been successfully solved?
- Define clear and measurable criteria to evaluate the effectiveness of the solution.
- Examples of success criteria could include:
- Cost reduction
- Increased revenue
- Improved customer satisfaction
- Enhanced operational efficiency
- Reduced time to market
- Higher employee engagement
- …
- Ensure that the criteria are specific, measurable, achievable, relevant, and time-bound (SMART).
- Scope of Solution Space: What are the boundaries within which the solution
must be developed?
- Define the scope to avoid scope creep and ensure that the solution remains focused on addressing the core problem.
- This could include factors such as budget, resources, timeframes, and any other relevant constraints.
- Clearly outlining the scope at the beginning helps in focusing efforts and avoiding unnecessary complexities and time wastage.
- Don’t assume that the others know everything and the scope is obvious; explicitly state it. Because different stakeholders may have different interpretations of the scope, leading to misalignment and confusion later in the process, understanding more about why they think that way can help clarify the scope.
- Why the scope is important?
- The larger the scope, the more complex the problem becomes, making it harder to solve effectively.
- A well-defined scope helps in allocating resources efficiently and prioritizing tasks.
- It ensures that all stakeholders have a shared understanding of the problem and the solution space.
- A smaller scope helps in managing expectations and avoiding misunderstandings, which quickly builds trust capital among stakeholders.
- Examples of scope definitions could include:
- Geographic boundaries (e.g., specific regions or countries)
- Target customer segments
- Product or service lines
- Timeframes for implementation
- Resource limitations
- …
- Constraints within Solution Space: What are the limitations or restrictions
that need to be considered when developing the solution?
- Identify any factors that may impact the feasibility or implementation of the solution.
- This is different from the scope, which defines the boundaries of the solution space. Constraints are specific limitations that must be adhered to within that space.
- Clearly outlining the constraints helps in developing realistic and achievable solutions. Like customers may have specific requirements or preferences that need to be taken into account. Understanding these constraints early on can help in developing solutions that are more likely to be accepted and implemented successfully.
- Then to make resource analysis
- Time and Budget are the most crucial ones, it’s impossible to satisfy
speed, cost and quality at the same time, so you have to make trade-offs
and then prioritize them (Fastest = Time is limited, Cheapest = Budget is
limited, Best Quality = Stability is required):
- Fast and Cheap = Low Quality
- Fast and High Quality
- Cheap and High Quality = Slow
- Different level of decision makers may have different tolerance levels for
time and budget constraints, so it’s important to understand their priorities.
- The higher the level of the decision maker, the more they may prioritize strategic objectives over operational constraints, such as time and budget.
- For example, a CEO may prioritize speed to market, while a CFO may focus more on budget constraints
- For example, a decision for a 9-month’s project cause high feedback loop cost and opportunity cost, so the decision-making is very important.
- Many problems include many hidden mental needs, and they may not be explicitly stated. Understanding these hidden needs can help in identifying potential constraints that may impact the solution. For example, a stakeholder may have limited budget but may not explicitly state it as he’s worried about being small minded.
- Good solutions should always consider these constraints to ensure feasibility and successful implementation, it make the proposal high possibility to be approved by decision makers.
- Questions to ask:
- How many people does it require?
- How much budget does it require?
- How long does it require to implement? (Absolute deadlines?)
- Time and Budget are the most crucial ones, it’s impossible to satisfy
speed, cost and quality at the same time, so you have to make trade-offs
and then prioritize them (Fastest = Time is limited, Cheapest = Budget is
limited, Best Quality = Stability is required):
- Examples of constraints could include:
- Budget limitations
- Resource availability
- Time constraints
- Regulatory requirements
- Organizational policies
- Technological limitations
- …
- Key Sources of Insight: What are the primary sources of information that
will be used to gather data and insights for problem-solving?
- Identify relevant internal (private and paid for premium) and external
(public and free) sources, the external should be baseline to study from the
get-go, such as:
- Internal reports and data
- Industry research and publications
- Expert interviews and consultations
- Customer feedback and surveys
- Competitive analysis
- Market trends and analysis
- …
- Having a clear understanding of key sources of insight helps in gathering relevant and reliable data to inform decision-making.
- It ensures that the problem-solving process is based on accurate and up-to-date information.
- Identify relevant internal (private and paid for premium) and external
(public and free) sources, the external should be baseline to study from the
get-go, such as:
The Hidden Complexity of Team Communication:
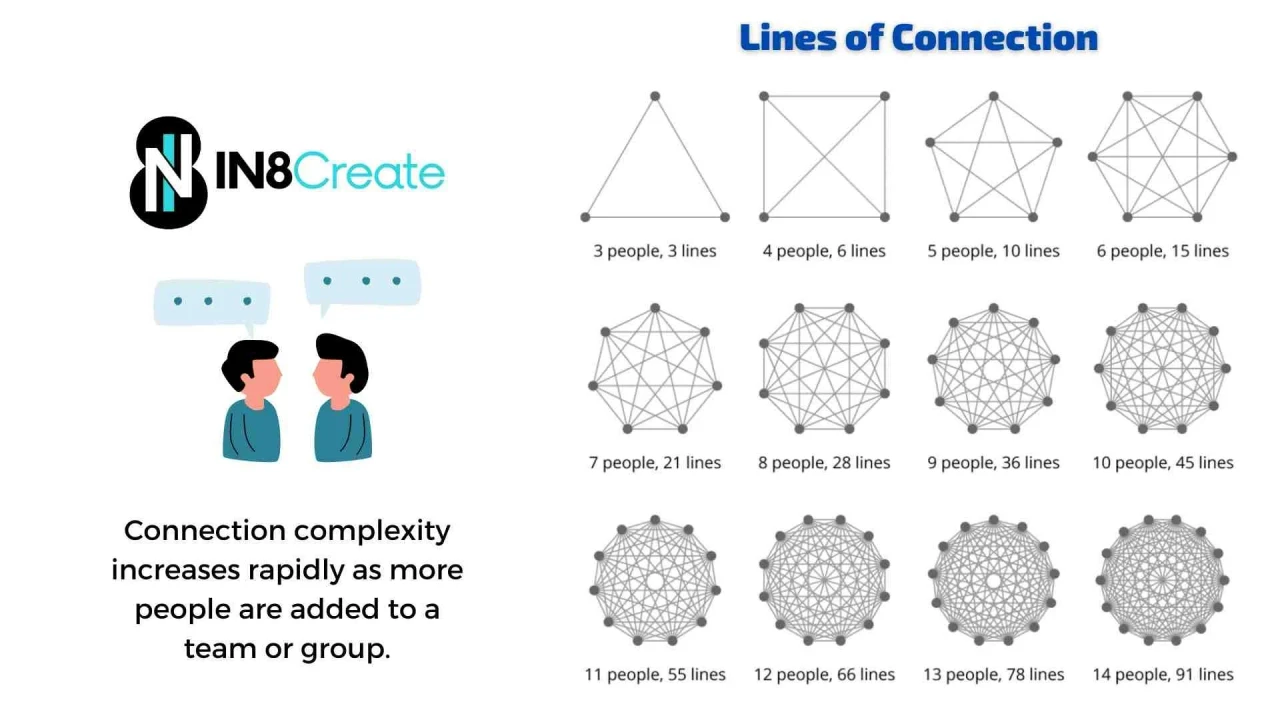
Connection complexity increases rapidly as more people are added to a team or group. Therefore, it’s crucial to identify and engage the right stakeholders early in the process to ensure smooth communication and collaboration.
If any step’s information isn’t clear, please ask more smart questions to clarify. Otherwise, you shouldn’t proceed to the next step like business analysis, consulting, or project management. Because “Garbage In, Garbage Out” (GIGO) always applies, meaning that poor-quality input will lead to poor-quality output, so ensure that each step is well-defined and understood before moving forward.
Conclusion
By following these 7 steps, individuals and organizations can approach problem-solving in a structured and effective way, leading to better outcomes and more informed decisions.