Suggested continuation from #281 and as was originally described in "Part B" of https://hackerone.com/reports/390929
If you agree, I can submit the suggested fix as a PR
Description
First, note that with the addition of default function parameters in ES2015, it is easy to evaluate arbitrary JS expressions if you have access to arg in new Function(arg, body), for example new Function("x=alert(2+2)","return x")
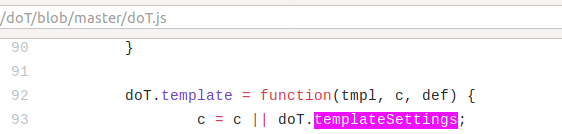
Next, note that calling doT.process({}) without specifying templateSettings (which is the intended way of using the function when not attempting to override defaults) will allow a templateSettings property to be taken from o's prototype:

So, with a previously exploited prototype pollution vulnerability, doT can be caused to run arbitrary code stored as a string in that prototype:
/*elsewhere*/
Object.prototype.templateSettings = {varname:"x=alert(1+1)"};
/* in app code */
const templates = require("dot").process({path: "./my_trusted_templates_that_I_wrote"});
templates.mytemplate(data); // Executes code specified by prototype
### Suggested fix
On line 45, highlighted above, replace `... o.templateSettings ? ...` with `... Object.prototype.hasOwnProperty.call(o,"templateSettings") ? ...`
### Aside - similar but unaffected property
^ Here, a similar issue could be present with `Object.prototype.varname` but upon closer inspection, I don't think it's a significant issue since doT users are prevented from omitting the varname property in normal doT usage
Suggested continuation from #281 and as was originally described in "Part B" of https://hackerone.com/reports/390929
If you agree, I can submit the suggested fix as a PR
Description
First, note that with the addition of default function parameters in ES2015, it is easy to evaluate arbitrary JS expressions if you have access to
arginnew Function(arg, body), for examplenew Function("x=alert(2+2)","return x")Next, note that calling

doT.process({})without specifyingtemplateSettings(which is the intended way of using the function when not attempting to override defaults) will allow atemplateSettingsproperty to be taken from o's prototype:So, with a previously exploited prototype pollution vulnerability, doT can be caused to run arbitrary code stored as a string in that prototype: